Did you know that protected Health Information (PHI) is extremely valuable to hackers, even more so than credit card data?
What is HIPAA compliance?
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) is a federal law for the United States of America. It was primarily established to:
- Improve portability and continuity of health insurance coverage. Portability means insurance coverage is maintained when an individual takes a job with a new employer
- Combat waste, fraud, and abuse in health insurance and health care delivery.This includes implementing the Privacy Rule, Security Rule, and BreachNotification Rule
- Promote the use of medical savings accounts by standardizing the amount that may be saved per person in a pre-tax savings account
- Improve access to long-term care services and coverage. This includes coverage of individuals with pre-existing conditions
- Clarify tax deductions for employers and other tax revenue items
See also: How Much Does HIPAA Compliance Cost?
See also: SecurityMetrics HIPAA Guide
Why we created the HIPAA Guide
Protected Health Information (PHI) is extremely valuable to hackers, even more so than credit card data. PHI and associated personally identifiable information (PII) can be used to make false insurance claims, gain access to prescription drugs, or target patients with healthcare-related scams.
Because of PHI’s value, hackers are determined to steal it. Healthcare practices are focused on caring for patients, which means information security can be neglected. These circumstances can contribute to devastating breaches with far-reaching consequences that sometimes include going out of business.
Our mission is to help organizations avoid the pain of a data compromise. As part of that mission, we created the HIPAA Guide to help businesses that handle PHI comply with HIPAA Privacy, Security, and Breach rules. On the path to becoming HIPAA compliant, these organizations could use a trustworthy guide.
At over 260 pages, the annual SecurityMetrics Guide to HIPAA Compliance is a detailed reference for any HIPAA Privacy Officer, Security Officer, or the people supporting their efforts. We highlight the areas that are quick and impactful, while providing outlines of concepts that may take more time to understand and implement.
Security Perspectives from the Field
As a team of auditors, we have the opportunity to collaborate on the HIPAA Guide. Keeping the Guide updated and accurate takes input from security assessors, penetration testers, forensic analysts, technical writers, graphic designers, and others–a process which takes months.
Included in this process is the writing of “Auditor Perspectives.” Our security professionals write personal perspectives on specific HIPAA topics, drawing on their experiences in the field. These sections include insights on topics like how to meet evaluation requirements, what good firewalls look like, password complexity, whether a healthcare organization should implement a SIEM (security information and event management), if encryption is reasonable, etc.
Here is an example of an auditor's perspective from the HIPAA guide:
What’s in the SecurityMetrics Guide to HIPAA Compliance?
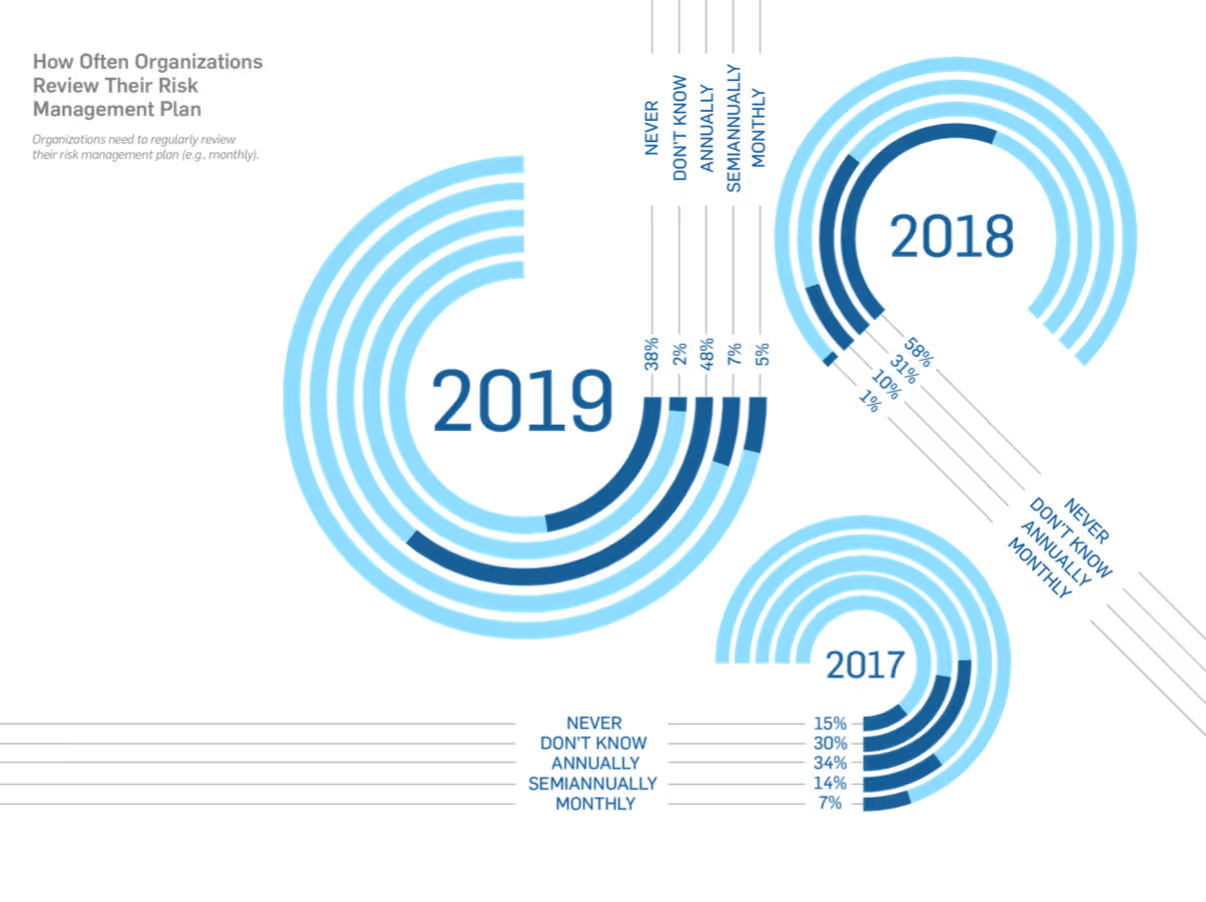
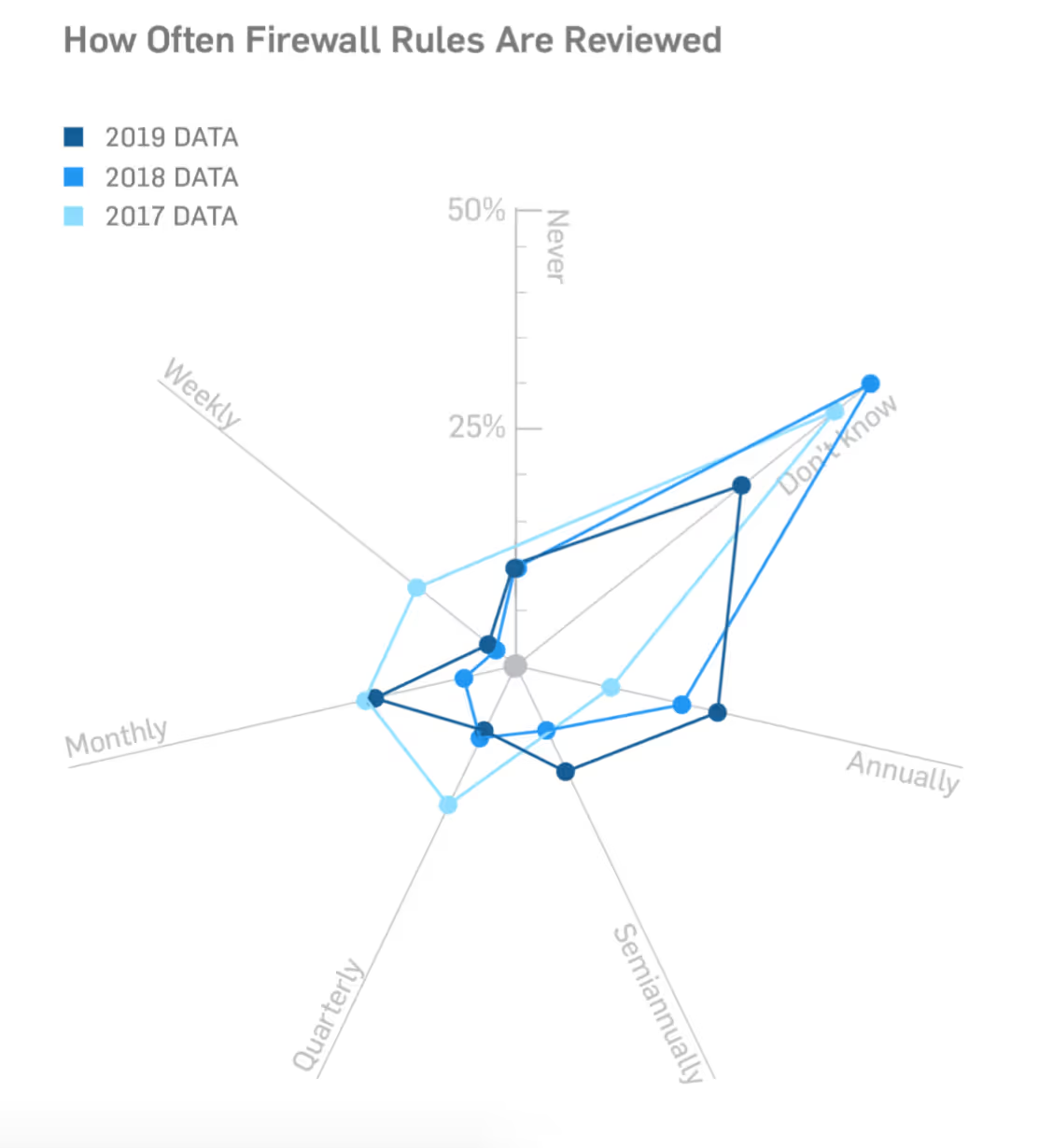
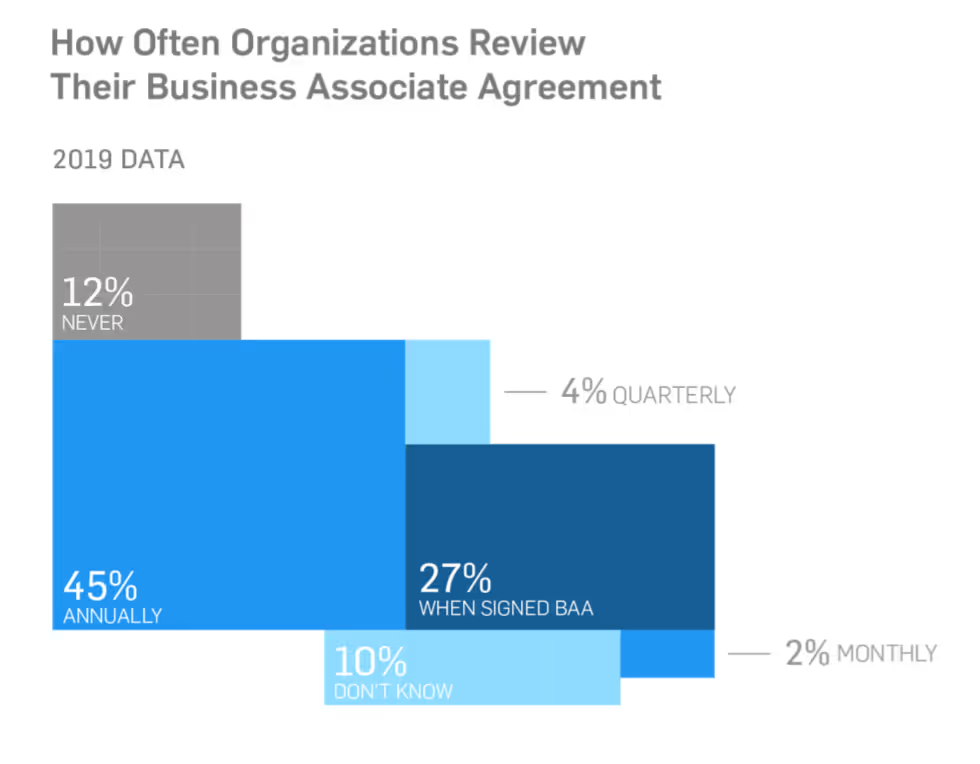
Every year, our HIPAA research team conducts surveys of HIPAA leaders at healthcare organizations to find out where organizations could use support and education, as well as to give context to our readers.
Our responses come from over 450 different healthcare professionals responsible for HIPAA compliance. These survey respondents mostly belong to organizations with fewer than 500 employees, but the resulting data is important to organizations of all sizes because almost all healthcare organizations share patient data with one another. When PHI is shared between two organizations, they impact each other’s security, regardless of size.
Here is a sampling of some of the graphs from the HIPAA Guide:
In addition to new survey data every year, the annual HIPAA guide includes help with:
- Incident response plans
- PHI encryption
- Business associate agreements
- Mobile device security
- Cloud security
- HIPAA-compliant emails
- Remote access
- Vulnerability scanning
- Penetration testing
Areas of compliance concern
HIPAA compliance is rarely straightforward. It isn’t a security framework or standard that lays out a series of boxes to check. HIPAA is a law that requires companies to have certain security controls in place without telling them how.
We give extra details and guidance on those areas that frequently give businesses trouble. For example, the law differentiates between “required” and “addressable” requirements within the Security Rule. This leaves many organizations wondering in what cases they need to apply certain security rules. As security professionals, we understand what security controls need to be in place to protect the confidentiality, integrity, and availability of electronic Protected Health Information (ePHI) and we include that information in this guide.
What health organizations say about our guide
Healthcare organizations report that they love the ease of use, structure, and accessibility of the 2020 SecurityMetrics Guide to HIPAA Compliance to assist with implementing security controls and training staff. Here’s what some of the HIPAA Guide users have to say:
"Thank you for providing the guideline for our business. It is less stressful knowing that I have the correct guide to improve our services to our patients and to protect our business." Nancy Wiseman, M.Ed., Ed.S., Vice President, Citrus Endodontics, P.A.
"This is the most comprehensive guide on HIPAA I have found." Crystal Hertz, National Health Foundation
"The HIPAA Guide is one of the best helps/tools/references. It's well organized and easy to understand for our medical office staff and providers." Hedy Haun, Sr. Process Analyst, Sharp HealthCare
"I loved SecurityMetrics. They have the best resources when it comes to PCI and HIPAA compliance and their customer service is unmatched." Jennifer M. Connell, Owner E2E Health Solutions, LLC
"SecurityMetrics Guide to HIPAA Compliance is really helpful, very informational and updated." Jeffrey Delos Reyes, Flow Health Outsourcing, Inc.
The HIPAA Security Rule
One of the reasons our annual HIPAA guide is so important is that for every requirement of HIPAA security, there are numerous differing opinions floating around out there regarding how to properly implement associated security controls.
In fact, if you want to start a nerdy debate, ask a group of security professionals how passwords should be implemented. After a lengthy (often heated) conversation with a lot of 5-dollar words you’ll be lucky to reach a consensus.
But if you use a straightforward guide with a well-rounded approach to best practices, supported by real-life auditor perspectives from the field to nuance your understanding of security controls in different environments, you can have more confidence in your HIPAA compliance efforts, train employees effectively, and ultimately–better protect patient data.






.svg)