The difference: HITRUST vs. HIPAA HITRUST is a compliance framework created by a private alliance of security industry experts and includes many aspects of HIPAA Security and Privacy Rules.
What is HIPAA?
HIPAA stands for Health Insurance Portability and Accountability Act. HIPAA is a US law that details, among other things, the data security and privacy provisions needed to ensure the confidentiality, integrity, and availability of protected health information (PHI).
HIPAA helps organizations avoid data breaches, cyberattacks, and crippling ransomware–all of which can stop a healthcare organization in its tracks and prevent it from helping patients.
Title II of HIPAA has two sections that deal with protecting data: the Security Rule and the Privacy Rule:
- Privacy Rule: Deals with keeping patient information private. Organizations can’t share PHI about a patient to anyone without the patient’s consent, except under certain circumstances.
- Security Rule: Deals with keeping PHI secure and away from hackers. Aspects of PHI like social security numbers are in high demand by criminals and are much harder to replace than credit cards.
See Also: HITRUST Assessment Basics
What is HITRUST?
HITRUST is the Health Information Trust Alliance. It was founded in 2007 to support organizations in all sectors, but especially health organizations, to reach information risk management and compliance objectives. In fact, according to the HITRUST Alliance, 81% of hospitals and health systems and 83% of health plans utilize the HITRUST Certification Standard Framework (CSF).
HITRUST was created to provide an option for the healthcare sector to address information risk management using a matrix of third-party assessments. The idea is to consolidate efforts and reduce the need for multiple reports, i.e., “assess once, report many.”
HITRUST includes elements from risk management frameworks like the Payment Card Industry Data Security Standard (PCI DSS), HIPAA, NIST 800-53, NIST CsF, and ISO 27001.
The “HITRUST approach,” along with HITRUST certification, gives vendors and covered entities a way to demonstrate compliance to HIPAA requirements based on a standardized framework. The ultimate goal of HITRUST certification is for businesses to effectively manage data, information risk, and compliance.
The difference: HITRUST vs. HIPAA
HITRUST is a compliance framework created by a private alliance of security industry experts and includes many aspects of HIPAA Security and Privacy Rules. The HITRUST Alliance seeks to provide organizations with a way to show evidence of compliance with a variety of mandated security controls.
HIPAA is a law that was enacted in 1996 by lawyers and lawmakers and is enforced by the US Department of Health and Human Services (HHS). All organizations that handle PHI must comply with HIPAA.
According to the HHS, "The HIPAA Privacy Rule requires that covered entities apply appropriate administrative, technical, and physical safeguards to protect the privacy of protected health information (PHI), in any form . . . This means that covered entities must implement reasonable safeguards to limit incidental, and avoid prohibited, uses and disclosures of PHI, including in connection with the disposal of such information."
HITRUST does not replace HIPAA, but it can provide measurable criteria and objectives for applying "appropriate administrative, technical, and physical safeguards."
Why do Healthcare Entities Choose to Become HITRUST Certified?
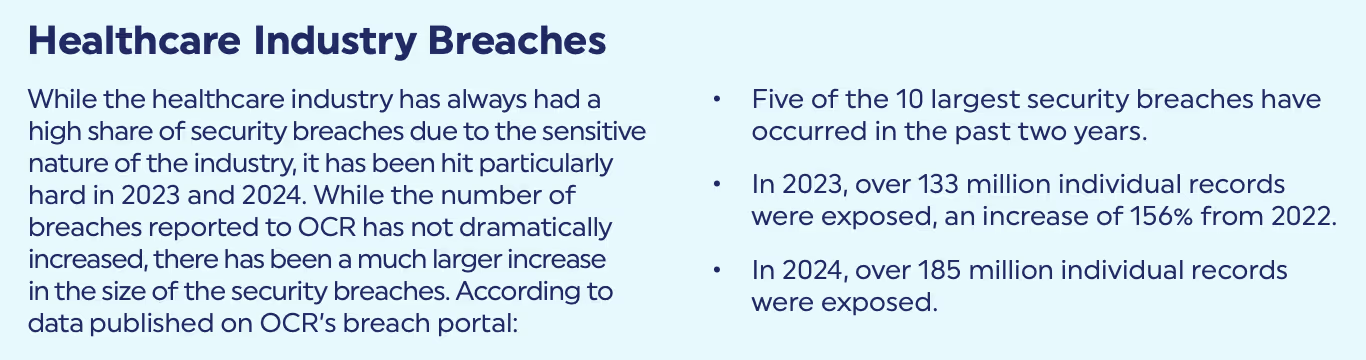
The Healthcare industry has a unique set of problems. Breaches are common and tend to be especially large (see image below). Many healthcare organizations choose to become HITRUST certified because they find the threat analysis process within HITRUST to be more effective in protecting them from security breaches.
Many Healthcare entities are required to become HITRUST certified by their larger organization or by their Business Associates. Whatever your reasons for becoming HITRUST certified, it’s important to choose a worthy HITRUST assessor. Check out this blog on common HITRUST FAQs for more information.
If you’re HITRUST certified, does that mean you’re HIPAA compliant?
No. HITRUST is widely accepted as a good approach for evaluating risk, but–as noted above–it does not replace HIPAA compliance or prove that an entity is HIPAA compliant.







.svg)