PCI DSS Requirement 4 focuses on protecting stored and transmitted card data.
PCI Requirement 4: Securing Your Networks
What do you do with your card data once you receive it? How is it transmitted to other areas? Are you securing these areas? These are all questions that can be related to PCI Requirement 4.
This requirement covers secure data transmission, especially when doing it over open and public networks. Businesses should be aware of how their card data is transmitted and through which networks.
“Build on the data flow diagrams discussed in the tips in Requirement 3.3. Know exactly where CHD is coming from and being sent to, inside and outside of your organization. Make sure your CHD is encrypted when transmitted over open public networks using strong and industry-accepted encryption technologies.”
(Ben Christensen, SecurityMetrics Senior Security Analyst CISSP | CISA | QSA)
Check out this PCI Requirement Four video for a concise summary of what you need to know.
Keep track of your PAN (Primary Account Numbers)
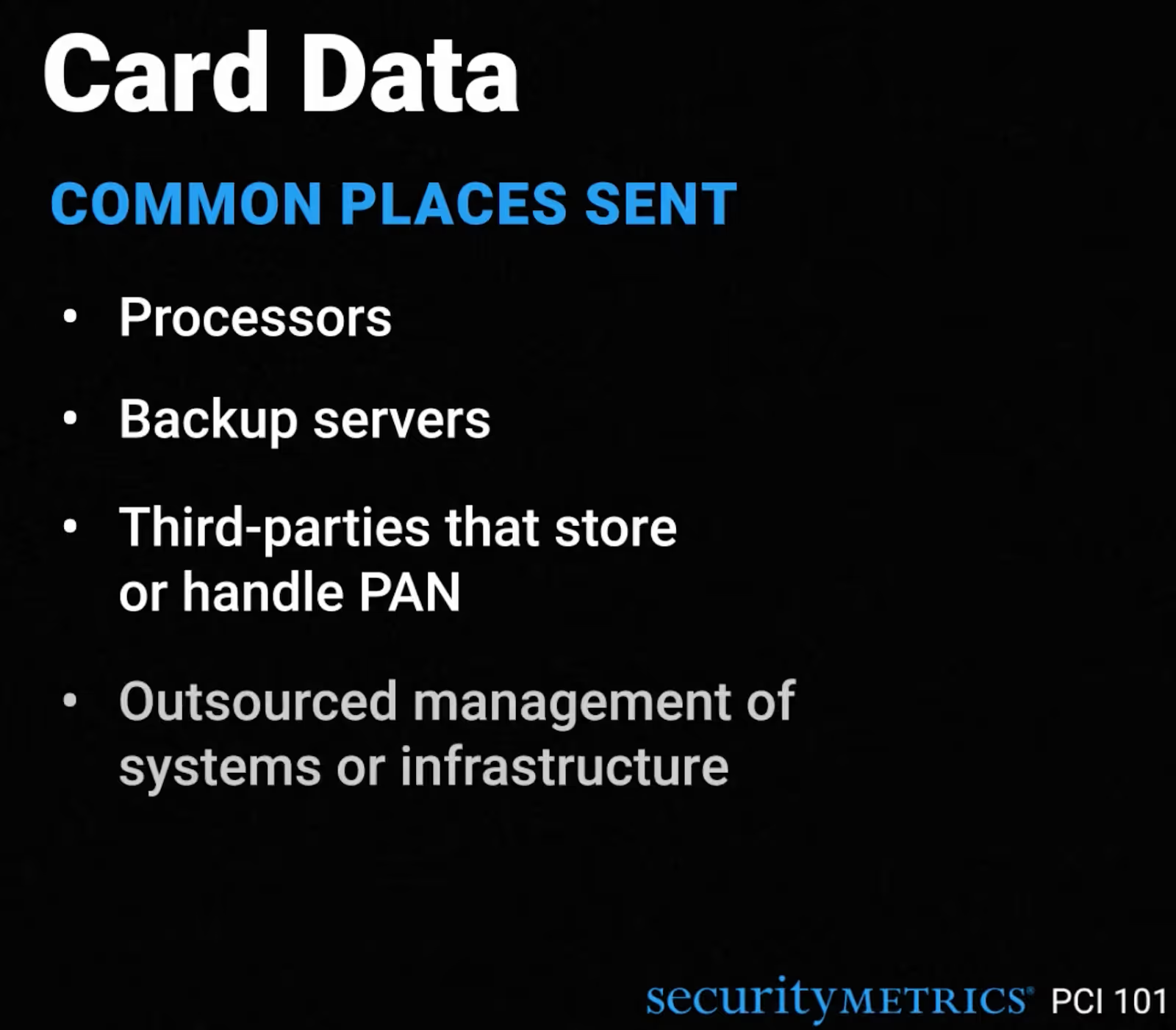
You need to identify where you send cardholder data. Information like Primary Account Numbers (PAN) and magnetic stripe data should be stored securely and be encrypted. Some common places PAN is sent include:
- Processors
- Backup servers
- Third parties that store/handle PAN
- Outsourced management of systems
- Corporate offices
See also: How Much Credit Card Data do You Store? (It’s More Than You Think.)
Stop Using SSL/TLS
“Some organizations may have a large number of TLS certificates. Start inventorying those now so that you can create a good method to start tracking their strength and expiration status. ” (Ben Christensen, SecurityMetrics Senior Security Analyst)
If your business is using SSL/TLS, you should stop and update as soon as possible. These latest versions of web coding have several vulnerabilities. You should contact your terminal providers, gateways, service providers, and acquiring bank to see if the applications and devices you use have this encryption protocol.
Applications that use SSL/TLS may include:
- POS/POI hardware terminals
- Virtual payment terminals
- Back-office servers
- Web/application servers
If you need to keep using SSL/TLS, here are a few tips to protect your data:
- Upgrade to a current, secure version of TLS configured not to accept fallback to SSL or early TLS
- Encrypt data with strong cryptography before sending over SSL/early TLS (i.e., use field-level or application-level encryption to encrypt data prior to transmission)
- Set up a strongly encrypted session first (e.g., IPsec tunnel), then send data over SSL within the secure tunnel
- Check firewall configurations to see if SSL can be blocked
- Check that all application and system patches are up-to-date
- Check and monitor systems to ID suspicious activity that may indicate a security issue
If you have existing implementations of SSL and early TLS, you need to have a Risk Mitigation and Migration Plan in place. This document will help you detail your plans for migrating to a secure protocol and the controls you have in place to reduce the risk.
See also: SecurityMetrics PCI Guide
See also: DROWN Attack and SSL: What You Need to Know
What You Need to Do to Meet PCI Requirement 4
There are a few things you can do to make sure you’re meeting PCI Requirement Four, including:
- Check all related device configurations for proper encryption.
- Check with vendors to make sure supplied POS/POI devices are encrypting data appropriately.
- Validate that POS/POI devices are not susceptible to any known exploits. Devices and software used to process credit cards need to be PCI DSS compliant.
- Review all locations where CHD is transmitted or received. Examine system configurations.
- Review all devices and systems to ensure you use appropriate encryption within your CDE. You must safeguard sensitive cardholder data during transmission over open, public networks.
- Use only trusted keys and certificates.
- Check inbound/outbound transmissions and verify that encryption keys and certificates are valid.
- Use secure configurations and proper encryption strengths.
- Do not support insecure versions or configurations. This means you will continually need to check for the latest encryption vulnerabilities and update as needed.
- Review and implement documented encryption standard best practices.
- Review and implement policies and procedures for sending and receiving credit card data.
- Examine system configuration and adjust encryption configuration as needed.
- Document, track, and inventory SSL and TLS certificates in use for the transmission of sensitive data across public networks (New for 4.0).
Additional Tips for Fulfilling PCI DSS Requirement 4
Here are a few other things to consider when fulfilling Requirement 4:
- Secure wireless network: ensure not just anyone can get into your wireless, and make sure all endpoints are secure.
- Update keys and certificates: verify that your security certificates are up to date and that your encryption keys are properly protected.
- Work with your service providers: you want to ensure they are also following proper procedures to make sure your data is safe.
- Train employees: make sure your employees are aware of what should be updated and what types of web encryption shouldn’t be used anymore.
Remember, it’s important to keep your data safe while you're storing and transmitting it. Make sure your web encryption is updated and all possible vulnerabilities are mitigated, as this is one way to ensure data protection.
Need help getting PCI compliant? Let’s see how you’re doing so far!








.svg)