If you’re wondering what this means for PCI requirement eight, this blog will cover key updates, how to strengthen your organization’s passwords and usernames, and how to implement MFA (Multi-Factor Authentication).
As of late 2025, reports indicate that 64% of organizations cite rising complexity as a major hurdle, and only about 32% feel fully ready for the new mandatory requirements. This means many organizations are scrambling to implement all of the future-dated PCI requirements.
If you’re wondering what this means for PCI requirement eight, this blog will cover key updates, how to strengthen your organization’s passwords and usernames, and how to implement MFA (Multi-Factor Authentication).
Key Updates to Requirement 8: The March 2025 Deadline
The most significant changes to access control, including those in Requirement 8, became mandatory on March 31, 2025, as part of the transition to PCI DSS v4.0.
The Non-Negotiables: Unique Credentials
The foundational principle of Requirement 8 is accountability, which is achieved through unique credentials assigned to every user who has access to sensitive cardholder data.
- Unique Usernames: Businesses must implement unique usernames for all personnel. Shared accounts eliminate accountability; your business cannot track exactly who performed a specific action within your systems when a pool of people share credentials.
- Unique Passwords: Personal and business security relies on using different passwords for different services. If one service is compromised, a hacker cannot use those credentials to access your critical business payment data.
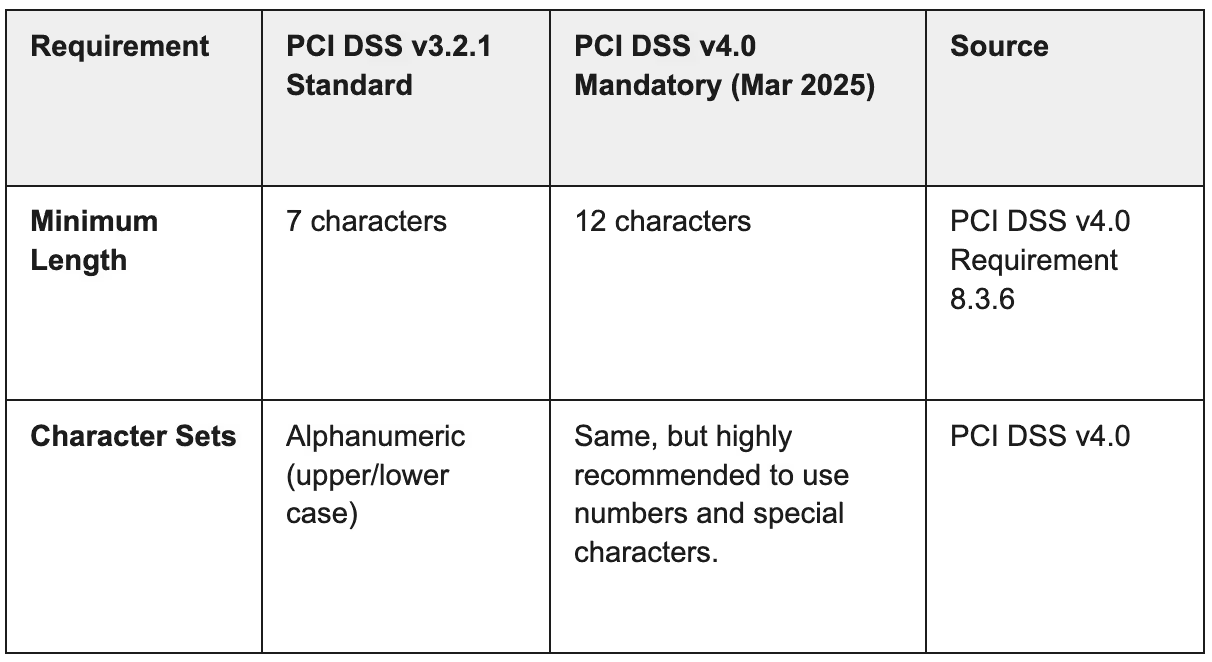
Setting Password Complexity to Meet PCI Requirement 8
If a password lacks complexity, it takes an attacker mere seconds to gain access to your environment using an automated brute-force attack.
The new, mandatory requirements under PCI DSS v4.0 reflect the urgency of stronger passwords:
Pro Tip: The longer and more varied the character formats, the more difficult it will be for an attacker to crack a password. Consider recommending passphrases—groups of random words (e.g., "We Never Drove Past Albuquerque?")—as they are easier for users to remember but harder for software to guess than complex, short passwords.
Layered Security: Multi-Factor Authentication (MFA)
System security should never be based solely on the complexity of a single password. No password should be considered uncrackable.
That is why implementing Multi-Factor Authentication (MFA) is a critical component of Requirement 8.
The MFA Requirement Expansion
The scope of MFA has been significantly expanded under the new standard:
- PCI DSS v3.2.1 required MFA only for remote access to the CDE and for administrative access.
- PCI DSS v4.0 expands this: MFA is now required for ALL access into the Cardholder Data Environment (CDE) (Requirement 8.4.2). This is a massive expansion of scope for many organizations, drastically improving protection against stolen credentials.
Configuring MFA requires at least two of the following three independent factors:
- Something only you know (e.g., a username and password, or PIN).
- Something only you have (e.g., a hardware token, smartcard, or mobile device for a one-time password).
- Something only you are (e.g., a fingerprint, ocular scan, or other biometric).
Pro Tip: Access to one factor must not grant access to another. If one factor is compromised, it does not affect the integrity of the others.
Defeating Brute-Force Attacks
Finally, to directly combat automated attacks, Requirement 8 mandates specific account lockout rules:
- Lockout Rule: Accounts must be locked after six consecutive failed login attempts.
- Lockout Duration: Accounts must stay locked for thirty minutes or until a system administrator manually resets the account.
This simple rule helps to mitigate brute-force attacks. If an attacker is only given six chances before being blocked, their attempts will almost certainly fail, leading them to move on to an easier target.
USDA Case Study: Phishing-Resistant MFA
To meet PCI requirements and combat sophisticated phishing, the U.S. Department of Agriculture (USDA) recently successfully deployed Fast IDentity Online (FIDO) authentication protocols to secure its network.
The USDA decided this was the best approach because seasonal workers could not rely on standard government security credentials. By leveraging a centralized identity management system, the USDA was able to integrate FIDO capabilities—which use device-bound cryptographic keys for authentication—across its core enterprise services, including Windows login and Single Sign-On (SSO) for over 600 internal applications.
This solution not only protected approximately 40,000 users from credential theft but also set a clear example for organizations moving toward the phishing-resistant MFA mandated by PCI DSS v4.0.
See also: New Multi-Factor Authentication Clarification and Supplement: The Principles You Should Know
Implement PCI Requirement 8 Now
With the March 31, 2025 deadline here for the mandatory PCI DSS v4.0 requirements—including the 12-character password minimum and expanded MFA—your business must act now to ensure compliance and avoid costly breaches.
Need help getting PCI compliant? Talk to us!

.avif)







.svg)