We outline the penetration testing process in detail and answer some of the most frequently asked questions related to this important security test.
Whether your business needs a penetration test for an industry compliance requirement, or because of a security incident, the process can seem overwhelming. We outline the penetration testing process in detail and answer some of the most frequently asked questions related to this important security test.
What is a penetration test?
A penetration test, or “pentest” for short, is a security assessment that simulates an attack by a malicious party on a network or application in order to identify security flaws. This test is coordinated ahead of time and executed with an attempt to avoid damaging any system. At the end of the test, your pentesting firm will provide you with a report that includes found issues and weaknesses along with suggestions for how to remediate them.
What is the difference between a pentest and a VA scan?
Many people wonder what makes a pen test different from a vulnerability assessment (VA) scan. There are a couple of big differences. First, a VA scan is an automated test. A penetration test is performed by qualified individuals that actually dig into the complexities of your network and actively try to exploit any vulnerabilities that they may discover.
A vulnerability scan typically only identifies vulnerabilities at a high level. This scan is not intended to exploit vulnerabilities, and produces an indication report. A pentester will dig deeper and attempt to identify root causes of vulnerabilities; they use their brain and creativity to gain access to databases and extract sensitive data.
One way to think about the difference between pen tests and VA scans is that VA scans are meant to regularly and quickly give you high-level insights into your network, while pentests go to a deeper level of security testing and are typically performed less often. A VA scan can be thought of as an x-ray–which is a little blurry, shows structure and fractures, but doesn’t show soft tissues and deeper complexities. A penetration test can be thought of as an MRI–which creates a 3D model of the body and provides a clear, orientated, dive into internal structures from many angles.
If you want to find the big problems in your applications or network architecture, you need a penetration test. A regular penetration test is a great way to ensure security as you continue to modify and improve systems.
Why do you need a penetration test?
Everybody wants to keep their businesses running and maintain a good reputation with their customers. Partnering with a qualified penetration testing firm that can work from the mindset of an attacker is the best way to truly improve the security of your systems.
Developers are very talented, but the question they ask while working is “How do I make it work,” not necessarily “How do I secure it?”
Only an autonomous, unaffiliated security team can really evaluate what can be broken, what harm can be done, and what can be done about it–without the unavoidable bias of a developer.
There are many reasons why a business might get a pen test. Perhaps they want to protect their customers or their reputation; both great reasons. Maybe they want to prevent downtime, damage, and humiliation in the face of a security incident. Maybe they’re releasing new software and want to make sure any changes made didn’t cause unanticipated problems. Or maybe they need to provide assurance to a 3rd party that they are secure–this can help limit liabilities if things go wrong.
Often, periodic penetration tests are needed to comply with legal or regulatory requirements like the Payment Card Industry Data Security Standard (PCI DSS) or the Health Insurance Portability and Accountability Act (HIPAA).
When do you need a pen test? How often should you get a penetration test?
We urge companies to get to the point where they use penetration testing as a security best practice. It’s a great corporate habit to get into. Pen testing is the best way to check the security of your internal processes; from IT, to development, to product design–you can make sure that departments are communicating and doing their jobs effectively, and that the “business as usual” process is working.
Other reasons you might need a penetration test: if you’re making major changes to your networks, installing new hardware like firewalls or servers with new operating systems in critical zones, reorganizing your whole network, adding new zones, moving to a new data center, or transferring data storage to a cloud.
It’s a good idea to periodically test any system that is handling sensitive data with a penetration test. And if you’re changing the software you generate or write by adding new features, refactoring or changing code, or upgrading to new versions, it may be a good time to do an application penetration test.
What are the different types of penetration testing?
Network penetration test
A network pen test is close to the hacking you see in Hollywood: someone is on the command line tool and is attempting to access your network and exploit services that may be open. Once access is gained, the attacker attempts to escalate privileges, get admin user permissions into an area of the network, then pivot and access more secure areas.
Web application penetration test
Web application penetration tests use the Internet to attack applications that may be visible to users. Your pen tester may test anything from a simple payment page to a full administrative console where you manage multiple customers, and they are looking for things like opportunities to escalate privileges and create an admin user in your web application. We may also be testing the API calls that are made from the application to see what extra information we can expose or even try to do things like dump the entire customer database, which may contain names, addresses, emails, and potentially even credit card or other sets of personal information.
Segmentation check
Oftentimes, you want to make sure that different systems don’t have access to sensitive areas on your network. Think of the Home Depot hack where the attackers got in through a contractor that had access to some internal areas from their side; then the attackers were able to pivot into Home Depot’s personal network because they didn’t have that network properly segmented. So we run checks to make sure that that information is kept separate and secure so that attackers can’t access it.
What compliance standards require a penetration test?
There are many industry standards that require a penetration test, including PCI, SOQ, HIPAA, GDPR, and more. There are also elective penetration tests that come after you’ve hardened your system it may be a great time to test how strong your environment is. Remember, if you make significant changes to your environment, you will need to penetration test again.
Who can be a pentester?
We often hear, “I’ve done software acceptance testing,” or “our developers did their own testing,” or “I did some automated code analysis with software, that should count as a penetration test right?” While there are some great automated technologies out there, the most important part of a penetration test is that the actual testing is performed by a real person. There is someone who can pivot, think, and look at little clues to decide whether to go different directions.
When it comes to the personality of a penetration tester, it’s not easy to find the necessary set of skills. Also, there are not many college courses or degrees in penetration testing. We’ve found that people who are good at pen testing are curious and creative. Plus, they have a strong technical background that gives them the ability to explore networks and applications and satisfy their curiosity for how things work. A good pen tester needs to be able to attack a wide range of environments that require a creative application of techniques to exploit weaknesses.
Not everybody can be a pentester. We at SecurityMetrics are lucky to have found pentesters with all of these qualities, and we continue to try to develop them in other candidates. It’s a unique person and personality that enjoys the penetration testing process. They’re not just people who wear hoodies and eat hot pockets. They’re actually pretty nice guys.
How can I tell a real pen test from a fake? How do I choose a pen testing firm?
Pen testers with more experience will be more expensive. Remember, you get what you pay for. Beware of a pentest firm that offers prices that just seem too good to be true. They probably aren’t doing a thorough job and will likely be doing mostly automated testing (e.g., running a VA scan). Look for a partner that has important credentials behind their name like CISSP, GIAC, CEH, or OSCP. And you can always ask a pentester to give you some of their past experiences; what kinds of things they’ve tested, etc.
What are the methodologies I should look for in a pen test team?
A pen testing team should be following industry best practices, standards, and methods such as OWASP, NIST, and other common cyber security standards when they are performing a test.
Your team may be looking at a SQL injection to get access to a database, they might be going after some broken authentication on the network, trying to pivot and gain admin access, or gain access to other users’ credentials. They may be going after some cross-site scripting (XSS) to potentially redirect customers or get more information from people using the system. They’re goal is to fingerprint the systems and then figure out, “How can I use this as intended but not as expected?” So there are a lot of different ways that the pentester might approach it, but ultimately you want to make sure that they’re following the industry best practices and communicating their testing methodology.
What are pentest tools? What tools will my pentesters use?
Oftentimes, we run VA scans before the manual part of your test ever starts to give your pentester some basic information. They aren’t familiar with your environment so they need a jumping off point to familiarize themselves with your network or web application.
You might also see a web proxy being used. These allow you to intercept web traffic before it’s sent to the server, so you can modify that traffic however you want, send it, and then check the response you’re getting. This gives you more control over what’s being sent through your browser.
Nmap and Metasploit are two other tools you may have heard of that are often used to scan the network and exploit any vulnerabilities discovered. The pentester may also use a password cracker, like hashcat, to try and bruteforce any authentication.
At SecurityMetrics, we also use a Raspberry PI or a virtual machine on the inside of your network–if performing an internal penetration test–which allows us to securely connect to the internal portions of your network and then test those internal portions without having the expense of a pentester on-site.
How much does a penetration test cost?
When you’re thinking about doing a penetration test, you also want to make sure you have a budget set aside.
Penetration testing prices vary widely according to the size and structure of a company. From small networks up to large zones and multiple large networks. Maybe you’re a Fortune 500, you’re going to be paying a lot more because you have a lot more assets. The list below is meant to give you a ballpark idea of what you should be looking at to budget for the penetration test:
- Small ~$8K
- 1 web app, 1 small network
- Medium ~$25K
- 3 web apps, 2 medium networks
- Large ~ $70K
- Multiple large web apps and/or network zones
- Multiple large web apps and/or network zones
How long does a penetration test take?
At SecurityMetrics, we have customers who take weeks and some who take a day. Some customers simply need a segmentation test, which isn’t defined by days or hours but rather how long it takes for them to get it finished. It really depends on the complexity of your environment and what your goals are.
What do I need to know before a pentest?
To prepare for your pentest, you need to answer some important questions: what is my motivation? What do I really want to find out? What are my compliance requirements? These answers will help your pentest provider know how to approach the testing.
Do you just want to know that you’re secure for your own peace of mind? Do you want to improve and evaluate your security posture? Do you need to increase security awareness for upper management in your company? Perhaps you want to justify spending for security expenses. Do you want to identify your controls and have confidence that they are working? Perhaps you are having a lot of security incidents and you want to reduce the frequency and the impact of those incidents.
Often there are third parties that require proof that you can be trusted with their data. Other times you are complying with legal and regulatory requirements: ISO, HIPAA, PCI, etc.
What is a penetration test like?
After you determine your goals, you need to match them up with your expectations. Are you looking for a deep dive into your systems? Do you want the pentester to go after a small number of vulnerabilities and see how far they can take them, or do you want them to look for a large number of vulnerabilities so you can improve the overall security of your systems?
You will hear the terms, “white hat,” “black hat,” and maybe even “gray hat.”
- Black hat: Malicious actor trying to break in and cause havoc.
- White hat: Someone on the inside with prior knowledge of the network or applications with permission to perform the test.
- Grey hat: Typically a gray hat hacker will have permission to test the system, but not have prior knowledge of the system.
Automated tools for discovery are useful because they provide vital information about the systems that a pentester can use in their attack simulation.
You should expect some noise or traffic during your test. Testers are not trying to hide or mask their attacks in any way like a real attacker might. They generally want to identify and exploit the issues as quickly as possible as penetration testers are on a clock.
You can also expect a detailed report with your security issues along steps to reproduce issues. The penetration tester should ultimately be able to help you improve your security by identifying these issues.
Authenticated vs. unauthenticated pentesting
Authenticated testing gives the pentesting firm greater access to your applications or your network. A true black hat hacker has all the time in the world to access your systems, but hired penetration testers are limited by time. Granting a penetration tester access to your systems can speed up testing so they can find as many vulnerabilities as possible.
Do I have to outsource my pen test? Or can I do an in-house pen test?
Many wonder if you can do an in-house pentest or whether you need to outsource a third party. This choice is influenced by whether or not you are trying to fulfill the requirements of a security standard or regulation. Yes, you can technically perform an “in-house” penetration test with an internal team; however, they need to have certain skills. Your team will need proficiency in testing, experience in how to view and explore a network, as well as familiarity with OWASP in order to know how to access applications and understand how they work.
How to prepare for a penetration test
You need to have an up-to-date network diagram and a data-flow map for your environment. You should have a list of active posts, which needs to be as current as possible.You should also know what services should be open through your network or available through your web application. You don’t necessarily need to share all of this information with the penetration testing firm, but it will help you be ready in case they run into an issue or need more information.
Many times a pentester will discover an available exposed surface, so knowing what should be available vs. what is actually available really helps you as a company to gauge how effective a penetration test actually was and how well it met your needs.
How to scope for a penetration test
Knowing your network helps with scoping. Ask yourself: where do we want to focus our testing? What should our scope include? Your scope should obviously include very critical systems that may impact security if any sensitive data is being stored. Maybe there’s an application that’s written specifically for your information that you want to have someone look at.
In the payment card space, there are specific areas that you are required to test: where credit card data is stored, processed, or transmitted, along with any systems that affect the security of those areas. You would want to make sure that you’re preventing hackers from pivoting into the sensitive cardholder data environment (CDE) from less sensitive areas. All perspectives–both internal and external–need to be tested.
- External perspectives include web facing applications that users can see.
- Internal perspectives are from within the network.
We have seen many compromises over the years where attackers get into a part of the network they’re not supposed to be in, and then pivot into a more sensitive area. So, to understand the internal exposure in your network is equally as important as to understand the parts that are outside-facing.
Remember–do you want to test network controls? Do you have a lot of applications you want to test? You should communicate this to the pentest company so they can scope out the work and give you a good estimate of time and what’s required to perform an effective and efficient test.
What to expect in the penetration test lifecycle
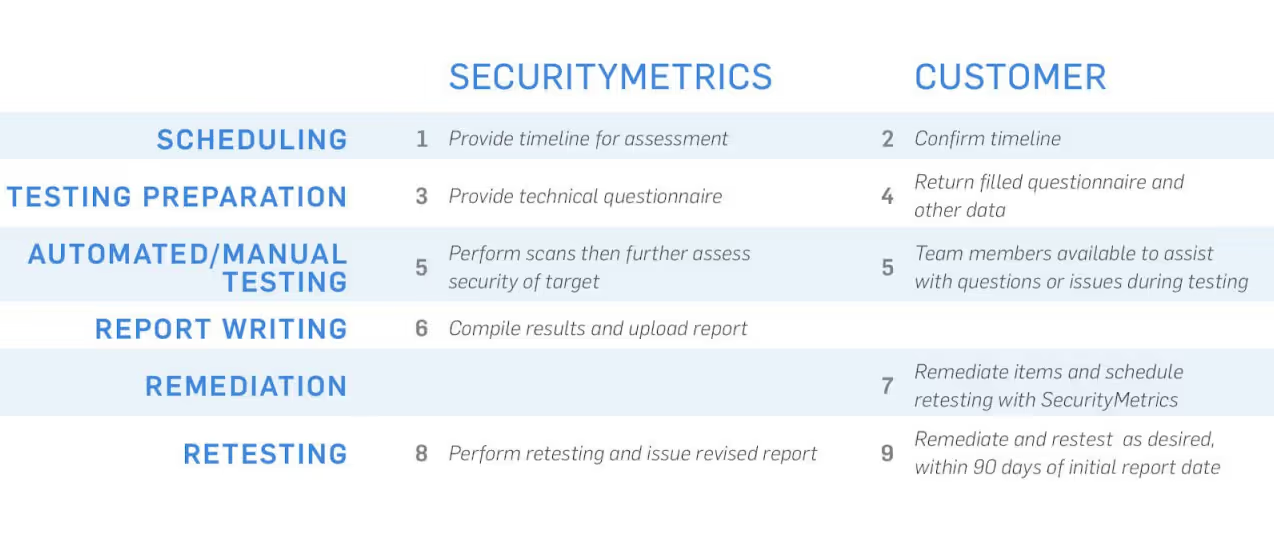
What are the steps of a pentest?
Preparation
At this stage, you want to make sure that the penetration test has been scheduled, and you will need to coordinate with the pentesting team and with individuals within your company to make sure they’re aware that the penetration test is going to be performed. You wouldn’t want your security operations center (SOC) getting alerts that you were being attacked and then have them accidentally shut off access to the test. This would delay the test and reduce the time available to test the environment.
Provide as much information as you can to the penetration tester. Let them know if they will need to be whitelisted so they can bypass external security appliances. There are cases where customers want us to test their perimeter, but most of the time these external appliances–given enough time–can be bypassed one way or another.
Automated pentest vs. manual pentest
Penetration tests require a lot of automated scanning. These scans are part of a pentest but do not constitute the whole thing. Typically, the scans serve to show us paths that we need to go down. Think about how the scans might affect your systems and pick a time of day when the traffic load level is low.
Think about whether the test can be completed on production systems, or if you need to have the pentester focus the tests on staging environments that you know have the same software and features but won’t affect any active customers or business operations.
There is a manual, human aspect to the test and we try our best not to impact your system. But depending on how code is written, problems may arise. To prevent issues, consider when these tests are taking place. Avoid scheduling a penetration test around your busy times, like around the holidays, for example. Make sure you plan enough in advance so you can schedule early in the year.
One thing you can do to help your pentest go smoothly is to make sure you’re available and responsive. If issues arise and are hindering the test, we want to help you fix them quickly so we can continue without taking up too much time. If we’re doing something that’s impacting your production environment we want to know right away so we can modify our testing platforms or patterns.
Also, make sure you’re not changing your environment in the middle of the pentest. If your pentester is in the middle of a test and something changes, that may cause issues and delays.
Your results: What’s in a penetration test report?
After the testing, your penetration test firm should provide you with a final report, and that report should have enough detail and be easy enough to read so that you can see and understand the issues they found. The Payment Card Industry Security Standards Council (PCI SSC) has released helpful guidance for companies who need to read and understand penetration test reports. Whether you are in the payments industry or not, this informational supplement is extremely helpful.
You will naturally want to know how security issues can be remediated, and the solutions will be included in the final report. Start by looking for an executive summary, sometimes called a “statement of the scope,” to get an explanation of how they did the test, what they tested, their methodologies, and limitations. This will give you a narrative to help you understand the exact steps your pentester went through. This summary should tell you the tools they used, and be very detailed. Your report should not be a one-page summary of IPs tested.
Now that your penetration test is complete and you’ve received your report, you should review it to see if the penetration tester was able to identify root causes of issues. Most of the time they can, but sometimes they can’t and are only able to observe a symptom of a bigger issue.
You will also want to create an improvement plan. Use the results to identify problems in your development life cycle. You want to make sure that you take advantage of this close-up look at your reports and the information that should be in them.
Penetration test remediation
Now you’ve reviewed the report and assigned tasks to your development or network team, you want to make sure you’re keeping up on security hygiene activities like installing patches and reconfiguring software. You also want to make sure that you’re updating the code for any applications you use. Many security issues are actually just outdated operating systems applications.
You want to make sure you are closing off any ports that don’t need to be open on your network. You want to restrict access as much as possible so you can still do business, but so that you don’t have anything extra open. Those are the avenues that attackers will utilize. You want to make sure you review the report thoroughly and quickly remediate all the issues.
Retesting after a penetration test
After remediation, you can send your test back over to the penetration testing firm. Your development team are not security experts. So it’s better to send the test back to the penetration firm so they can retest those fixes that you’ve implemented and make sure that they were done correctly and maintain the security of your environment as intended.
Occasionally organizations may implement something and send it to the pen test team. If the pen test team still finds the same issue, the fix was not broad enough. So, retesting is very valuable and helps make sure that fixes are implemented correctly.
After your penetration test
Now you can take a big sigh of relief. The test is over and you’ve remediated the issues.
As a company, you should now focus on making sure future tests are good experiences. Make these process and policy changes so you can avoid future vulnerabilities. As you find issues during the pen test, it’s wise to review how you could have avoided these issues and then incorporate your findings into “business as usual.” Use this knowledge to give additional training to developers and network engineers. Ask yourself questions like, do my developers and network engineers have enough time and resources to be successful in designing applications and systems?
It’s critical that you stay current on software updates. We often see companies that have the attitude of, “We’re done, so we don’t have to think about it for another year,” and then go back to their normal operations after a pentest without implementing regular updates or application/port scanning.
You’ll also want to consider your schedule for the year. You may want to schedule more of a time cushion for the end of your test, especially if you’re fulfilling a regulatory compliance requirement. A good rule of thumb is to start 3 months early so you can be prepared for compliance cycles.
Choosing a penetration testing firm
You want a pentesting company that will be a partner in security and will be easy to work with. Review the qualities listed earlier in this blog so you can screen pentest partners. You both need to be comfortable giving and receiving feedback from one another, so you can improve processes on both sides.
At SecurityMetrics, we communicate through a pen test coordinator. It’s a great way for clients to interact with the pentest team more often. We find that utilizing a human project management interface makes the entire process simpler, faster, and a better experience for all parties.
Remember that preparation is essential for a successful test. Most clients want to make sure they’re ready for the pentest, which helps things run a lot smoother. Your penetration testing firm should be seen as a partner; they shouldn’t be seen as adversarial. The goal for everyone involved is to improve the security of your company. You should focus on sharing information in a timely manner to help facilitate good, open communication on both sides.
One word of advice: remediation often takes a lot longer than you think it will. Sometimes it’s hard to remediate issues if your systems aren’t quite completed, but you can always plan for the next test cycle.
Finally, you want to make sure that you’re scheduling penetration tests when they make sense for you as a business. It’s always better to do a little bit more and go a little bit further with the penetration test versus just trying to scrape by with the bare minimum required. Also, when you make big changes to your network or an application or you release a new product, you want to make sure you have tested the changes thoroughly before they go live so they don’t introduce any live vulnerabilities into your systems.
What qualifications do SecurityMetrics pentesters have?
You should look for certain certifications when choosing a pentester. SecurityMetrics QSAs have CISSP and OSCP certifications, where the testers are certified against the standard. SecurityMetrics also holds its own testing program once a year where QSAs go up against their own servers to determine any vulnerabilities and the effective rate of exploiting them. Sometimes penetration testing firms are doing as little as possible to sign you off. SecurityMetrics QSAs want you be safeguarded against threat actors, so they take your pentest seriously.
If you have questions about penetration testing or would like a quote request for a pentest, please contact us here.







.svg)