Regular vulnerability scans are a critical preventative security control as they detect and assess known weaknesses that may be opening up your systems, applications and networks to undue risk of intrusion. Vulnerability scanning is not penetration testing.
*This article was taken from our HIPAA Guide. For more information on this topic, download our free HIPAA Guide.
“Tools used for audit logging and log analysis are called system information and event management (SIEM) solutions.”
A proper defense-in-depth strategy will consist of both preventative controls and detective controls designed to reduce the risk, severity, and cost of a data breach. Preventative controls like system hardening, vulnerability scanning, patching, intrusion prevention, etc., help to prevent unauthorized data or system access while detective controls such as log analysis and file integrity monitoring are designed to quickly identify a security compromise to help mitigate the effects of the intrusion.
Regular vulnerability scans are a critical preventative security control as they detect and assess known weaknesses that may be opening up your systems, applications and networks to undue risk of intrusion. As new vulnerabilities are constantly being discovered, it is important that these scans be performed often (monthly or quarterly) to identify weaknesses in your organization’s security posture. Then allow IT staff to address the vulnerabilities before they can be exploited by attackers.
Vulnerability scanners will often assign a risk value to each identified vulnerability (usually based on the Common Vulnerability Scoring System). Organizational vulnerability management policies and procedures should clearly define how IT staff are to rank the severity of identified vulnerabilities. Policies should also set clear expectations of the timeline for addressing or remediating the vulnerability based on the risk the vulnerability poses to the organization.
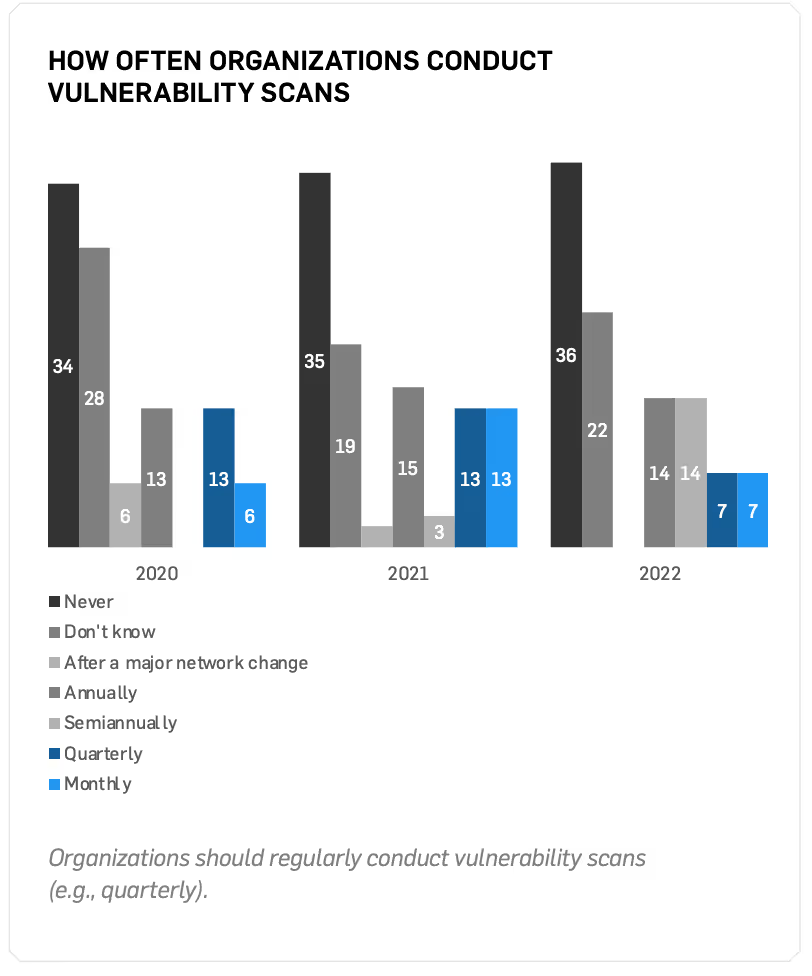
It is recommended that management takes an active role in the organization’s vulnerability management program. Too often, important day-to-day administrative tasks (e.g., IT fires) receive priority over critical preventative security measures as there often is no immediate consequence to failing to perform these tasks.
VULNERABILITY SCANNING VS. PENETRATION TESTING
Some people mistakenly think that vulnerability scanning is the same thing as a professional penetration test.
Vulnerability Scanning is not Penetration Testing.
Here are the two biggest differences:
- A vulnerability scan is automated, while a penetration test includes a qualified individual who digs into the complexities of your network and actively tries to exploit its vulnerabilities.
- A vulnerability scan typically only identifies vulnerabilities at a high-level, while a penetration tester digs deeper to identify the root cause of the vulnerability that allows access to secure systems and stored patient data.
Vulnerability scans offer great weekly, monthly, or quarterly high-level insight into your network security, while penetration tests are a more thorough way to deeply examine network security.







.svg)