System logs are part of HIPAA compliance and specifically mentioned in two different requirements.
Audit logs make it easier to detect problems in organizational security.
System logs are an important part of HIPAA compliance under the Security Rule. They are specifically mentioned in two different requirements and inferred by others. Logs are recorded pieces of information regarding the actions taken on computer systems such as office computers, electronic health record (EHR) systems, servers, printers, and firewalls.
Logs make it easier to look after the security of simple (single practice) and complex (hospital) networks. They’re also essential for business associates who could impact electronic protected health information (PHI) security.
How? Here’s a short list of what system event logs can be set up to record:
- When workforce members log in
- The number of failed login attempts on a computer
- The last time you conducted a software update
- Who downloaded a new program and when
- When you changed your password
- Who logged into the EHR at a certain time
- What information was accessed by the person logged in
- What ePHI was changed and by whom
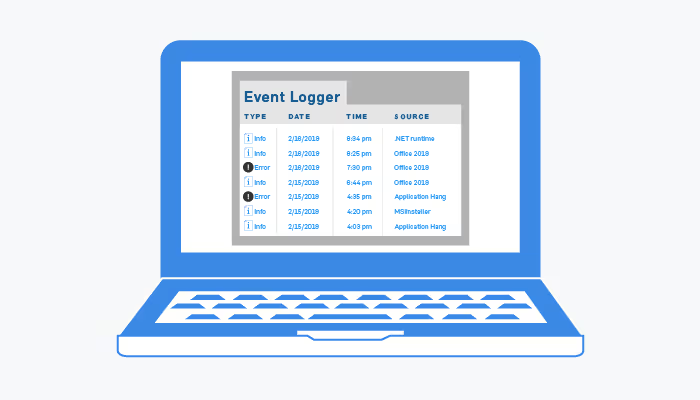
We’re going to look at two specific types of system logs can help you with HIPAA compliance: access logs and event logs.
If you assign unique IDs to your workforce members (as required by HIPAA), access logs allow you to know when an individual takes an action on a system.
For example, if I logged into my computer with my username and password at 9:05 this morning, the event, date, and time should be recorded by my operating system’s logging software and saved in a giant database of all the actions taken on my computer. If I also reviewed John Smith’s health information, that action should be logged by my EHR.
Event logs generally refer to significant markers in your logs. These markers indicate actions that could be related to breach or attempted breach activity. They might even generate alerts to let security personnel know of the incident so they can follow up and take action, if needed.
When would I use an access or event log?
Monitoring and analyzing user and system activity can help you understand ordinary patterns and detect irregular actions. For example, if Sally’s regular work hours are 8:00 am to 5:00 p.m., but she accesses patient data at 3:00 a.m., when no one is in the office; this would be considered an irregular action, and an alert should be generated.
If your systems are breached, logs help forensic investigators find out how hackers got into your system and what data was exfiltrated, so you can close the holes and avoid future attacks. Without reliable logs to prove what was impermissibly accessed, investigators must assume that all patient records were accessed and stolen.
See also: HIPAA Compliant Emails 101
HHS press releases offer high-level insight into what causes breaches and how they result in settlements or civil monetary penalties (CMPs). For example, in a press release about the Memorial Healthcare Systems (MHS) $5.5 million HIPAA settlement, HHS stated that “MHS failed to implement procedures with respect to reviewing, modifying and/or terminating users’ right of access, as required by the HIPAA Rules. Further, MHS failed to regularly review records of information system activity on applications that maintain electronic protected health information.”
In this case, the credentials of a terminated employee were used to access ePHI almost every day for five years and affected 80,000 individuals. Logs could have informed MHS IT staff which employees were accessing ePHI, on what day, and what other records they accessed. When combined with mature termination and user access review procedures, properly-implemented logging and alerting would have identified improper access of ePHI.
What do HIPAA regulations say about system logging? What are HIPAA compliant system logs?
Event, audit, and access logging are required for HIPAA compliance. HIPAA requires you to keep logs for at least six years. These three HIPAA requirements apply to logging and log monitoring:
- § 164.308(a)(5)(ii)(C): Log-in monitoring (Addressable). [Implement procedures] for monitoring log-in attempts and reporting discrepancies.
- § 164.312(b): Audit controls (Required). Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use ePHI.
- § 164.308(a)(1)(ii)(D): Information system activity review (Required). Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports.
During your security assessment, your assessors should ask for your access and system audit logs. They will be looking to validate that you are storing them for at least six years, that all pertinent information is included, and that you conduct a meaningful daily review.
An analysis tool can simplify your daily log review. In most organizations, manual log reviews are not practical because logs are so extensive that it’s all but impossible to parse them manually on a daily basis.
If you aren’t already collecting logs, get started now!
When setting up your systems to record logs, keep in mind these things:
- Collect logs from every system, application and program.
- Consolidate logs on a centralized logging server that is protected by security controls such as role-based access control and file integrity monitoring.
- Include logging servers in your data backup plan.
- Implement a log analysis tool (or SIEM) or subscribe to a Security Operations Center for a real-time review of logs with alerting of staff for suspicious behavior.







.svg)