2017 was a year marked by massive hacks like Equifax, rampant malware like WannaCry and Petya, notable vulnerabilities like KRACK, as well as changes to and guidance about the Payment Card Industry Data Security Standard (PCI DSS).
What can we learn about PCI compliance from 2017 data breach trends?
Noncompliance to PCI requirements
2017 was a year marked by massive hacks like Equifax, rampant malware like WannaCry and Petya, notable vulnerabilities like KRACK, as well as changes to and guidance about the Payment Card Industry Data Security Standard (PCI DSS).
But one thing stays the same year after year; complying with the PCI DSS makes organizations more secure. Failure to comply with even one of the PCI requirements can set a company up for inevitable data breach and theft. Our Forensics department has compiled statistics from their own PCI data breach investigations in 2017. This PCI Data Breach Visualization shows which specific failures in compliance contributed to the data breaches our Forensics department investigated.
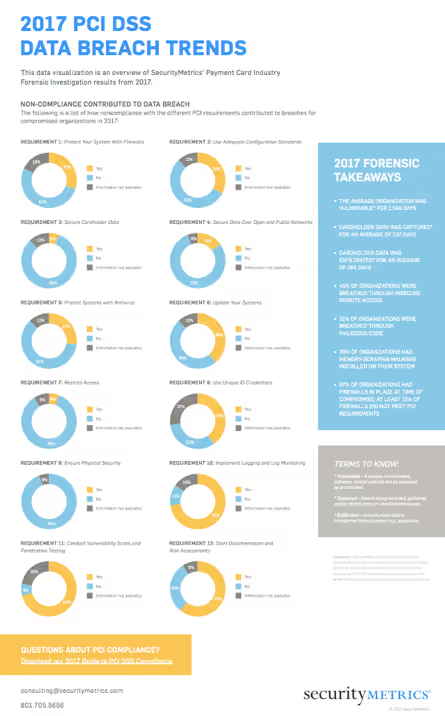
Most common contributors to a data breach
At a rate of 73% of all investigated breaches at SecurityMetrics, noncompliance with PCI requirement 10 “Implement Logging and Log Monitoring” was the issue most frequently associated with a data breach.
Log monitoring systems (e.g., Security Information and Event Management [SIEM] tools) track network activity, inspect system events, alert of suspicious activity, and store user actions that occur inside your systems. They can help warn you about a data breach, providing you with data known as event logs, audit records, and audit trails. Regular log monitoring means a quicker response time to security events and better security program effectiveness.
In second place for contribution to data breaches is noncompliance with PCI requirement 11, “Conduct Vulnerability Scans and Penetration Testing.” These scans and tests are critical for finding vulnerabilities and testing your in-place security measures. There are different types of vulnerability scans and penetration tests depending on your business or PCI audit needs.
2017 data breach trends: forensic data takeaways and tips
The average organization was vulnerable for 1,549 days
- The “window of vulnerability” is the time during which a system, environment, software, and/or website could potentially be exploited by an attacker.
- To reduce the window of vulnerability, implement and monitor standard security controls as found in the PCI DSS. Testing your security through traditional means like penetration testing and vulnerability scanning is a great place to start.
Cardholder data was captured for an average of 237 days
- This is the window of time during which data is being recorded, gathered, and/or stored from an unauthorized source.
Cardholder data was exfiltrated for an average of 264 days
- “Exfiltration” is the unauthorized transfer of data from a system (e.g., exporting).
45% of organizations were breached through remote access
- Remote access remains one of the most common hacking vectors because businesses often configure their remote access application insecurely.
- Limit employee access to remote access and implement multi-factor authentication.
21% of organizations were breached through malicious code
- Hackers use cross-site scripting (XSS) and other methods to introduce or “inject” malicious code.
- Run external vulnerability scans and talk to your web developer to make sure your site is securely coded.
39% of organizations had memory-scraping malware on their system
- Memory-scraping malware scans a device’s memory (e.g., a point of sale device) for personal information (e.g., SSNs and account numbers) and cardholder data.
- Make sure intrusion detection and prevention systems (IDS/IPS) are in place. Know where sensitive data resides (e.g., PANscan®), and restrict access to only those who absolutely need it (e.g., role-based access control).
97% of organizations had firewalls in place at time of compromise, but at least 15% of firewalls did not meet PCI requirements
- Make sure firewalls are configured correctly and assign someone to monitor your firewall logs daily. You need to document your firewall-related policies and procedures, as well as regularly review and test your firewall rule sets.
Now is the time to look back at forensic lessons and apply them to your current security practices. You can look forward to increased security in 2018 if you adjust your security practices to more closely follow the Payment Card Industry Data Security Standard.








.svg)