Discover what the difference is between a penetration test and a vulnerability scan.
Pentesting vs vulnerability scanning: two very different ways to test your systems for vulnerabilities
Penetration testing and vulnerability scanning are often confused for the same service. The problem is, business owners purchase one when they really need the other. Let me explain pentesting vs. vulnerability scanning.
A vulnerability scan is an automated, high-level test that looks for and reports potential vulnerabilities. A penetration test is a detailed hands-on examination by a real person that tries to detect and exploit weaknesses in your system.
Let’s dive a little deeper.
What is a vulnerability scan?
Also known as vulnerability assessments, vulnerability scans assess computers, systems, and networks for security weaknesses, also known as vulnerabilities. These scans are typically automated and give a beginning look at what could possibly be exploited.
High-quality vulnerability scans can search for over 50,000 vulnerabilities and are required as per PCI DSS, FFIEC, and GLBA mandates.
Vulnerability scans can be instigated manually or run on a scheduled basis, and will complete in as little as several minutes to as long as several hours.
Vulnerability scans are a passive approach to vulnerability management, because they don’t go beyond reporting on vulnerabilities that are detected. It’s up to the business owner or their IT staff to patch weaknesses on a prioritized basis, or confirm that a discovered vulnerability is a false positive, then rerun the scan.
To ensure the most important vulnerabilities are being scanned for, vulnerability scans should only be conducted by a PCI Approved Scanning Vendor (ASV).
Vulnerability scan reporting
After a vulnerability scan completes, a detailed report is created. Typically, these scans generate an extensive list of vulnerabilities found and references for further research on the vulnerability. Some even offer directions on how to fix the problem.
The report identifies potential weaknesses, but sometimes includes false positives. A false positive is when a scan identifies a threat that’s not real. Sifting through reported vulnerabilities and making sure they are real and not false positives can be a chore but one that must be done. Luckily a good scanner will rank vulnerabilities into risk groups (typically high, medium, or low) and will often assign a “score” to a vulnerability so you can prioritize your search efforts on discovered items starting with those of the highest potential risk.
Benefits of a vulnerability scan
- Quick, high-level look at possible vulnerabilities
- Very affordable (~$100 per IP, per year, depending on the scan vendor)
- Automatic (can be automated to run weekly, monthly, quarterly, etc.)
- Quick to complete
Limitations of a vulnerability scan
- False positives
- Businesses must manually check each vulnerability before testing again
- Does not confirm that a vulnerability is exploitable
What is a penetration test?
A penetration test simulates a hacker attempting to get into a business system through hands-on research and the exploitation of vulnerabilities. Actual analysts, often called ethical hackers, search for vulnerabilities and then try to prove that they can be exploited. Using methods like password cracking, buffer overflow, and SQL injection, they attempt to compromise and extract data from a network in a non damaging way.
Penetration tests are an extremely detailed and effective approach to finding and remediating vulnerabilities in software applications and networks.
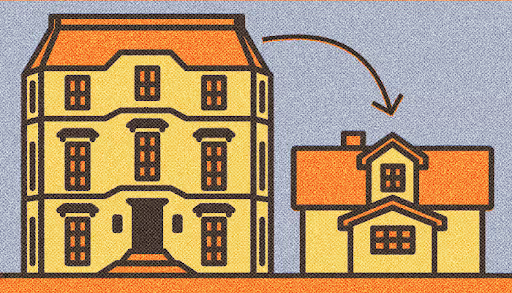
A good way to illustrate the benefits of a penetration test would be to use an analogy from the medical world. When something is wrong inside your body you can go get an X-ray to help diagnose your problem. The image produced by a simple X-ray machine can detect an obvious break in bone structure but is fuzzy and not good for seeing soft tissue damage. If you really want to find out in detail what might be going on inside a body, you need to have an MRI done that results in a detailed 3D model of bone and soft tissues together. That is similar to the difference between a simple vulnerability scan (fuzzy X-ray) and a penetration test (detailed MRI).
If you really want to find deep issues in your application or network, you need a penetration test. And if you modify your systems and software over time, a regular penetration test is a great way to ensure continued security.
See also: SecurityMetrics PCI Guide
Because of this level of detail, penetration testing is often a requirement in many security standards (PCI DSS, HIPAA, FedRAMP, SOC 2 Type2, etc).
The cost of a penetration test is usually between $15,000 to over $70,000, but it depends on the number of IP’s tested and the size of web applications evaluated.
Learn more about the cost of penetration testing.
The main aspect that differentiates penetration testing from vulnerability scanning is the live human element. There is no such thing as an automated penetration test. All penetration tests are conducted by very experienced, very technical, human beings.
Penetration testers are well versed in:
- Black hat attack methodologies (e.g., remote access attacks, SQL injection)
- Internal and external testing (i.e., perspective of someone within the network, perspective of hacker over Internet)
- Web front-end technologies (e.g.,Javascript, HTML)
- Web application programming languages (e.g., Python, PHP)
- Web APIs (e.g., restful, SOAP)
- Network technologies (e.g, firewalls, switches, IDS)
- Networking protocols (e.g., TCP/UDP, SSL)
- Operating systems (e.g., Linux, Windows)
- Scripting languages (e.g., Python, Perl)
- Testing tools (e.g., Nessus, Metasploit)
In short, penetration testers provide a deep look into the data security of an application and/or an organization.
Penetration Test Reporting
Typically, penetration test reports are long and contain a description of attacks used, testing methodologies, and suggestions for remediation.
Benefits of a penetration test
- Live, manual tests mean more accurate and thorough results
- Retesting after remediation is often included
- Rules out false positives
- Annual test, or after any significant change
Limitations of a penetration test
- Time (1 day to 3 weeks)
- Cost ($15,000 to $70,000)
Pentesting vs vulnerability scanning: Which is better?
Both tests work together to encourage optimal network and application security.
Vulnerability scans are great weekly, monthly, or quarterly insight into your network security (the quick X-ray), while penetration tests are a very thorough way to deeply examine your network security (the periodic detailed MRI).
Yes, penetration tests are expensive, but you are paying a professional to examine every nook and cranny of your business the way a real world attacker would, to find a possibility of compromise.
Schedule some time to discuss a penetration test for your business.





.svg)