Learn how to help your employees be better prepared to fight against social engineering tactics.
Social Engineering Training: What Your Employees Should Know

Learn how to train your employees to combat social engineering attacks.
What is social engineering? Social engineering refers to how criminals manipulate people into giving them private data such as bank information or credit card numbers.
Social engineering is a popular technique because criminals can bypass the technical side of security, such as firewalls, vulnerability scanning, and penetration testing, and get information directly from an individual. Because of its popularity and increasing sophistication, social engineering is a huge vulnerability to businesses since all employees are susceptible to social engineering attempts. This is why training your workforce on social engineering should be one of your top priorities.
Social engineers use email, SMS messaging, and phone calls to get information. Sometimes they will even seek access to a physical location and rely on other employees to let them into an area or leave sensitive data in the open.
Common examples of social engineering include:
- Phishing: Emails, ads, SMS messages, or even websites created to look like they come from reliable sources. Interacting with these emails, ads, SMS messages, or websites gives criminals access to information.
- Vishing: phone calls or voice mails that try to convince victims to reveal personal information to avoid fines, arrest, or other consequences.
- Baiting: Giving a victim a false promise or a prize to manipulate them into a trap so that a criminal can steal personal data or inflict a system with malware.
- Tailgating: leveraging trust or distraction to gain access to a secured physical space. For example, following closely behind someone so that they hold the door open for you.
- Using deepfake software to look or sound like a trusted persona is also becoming an increasingly popular social engineering tactic.
Social engineering is one of the easiest ways to steal data, especially if employees haven’t been trained on how to recognize and combat it. Social engineers make themselves look like they belong to a company, and can walk into an organization, steal data, and walk out in a very short amount of time.
See also: 9 Ways to Social Engineer a Hospital
Since social engineering targets the workforce, the best way to combat it is to train your employees.
Can you spot the error in this phishing email?
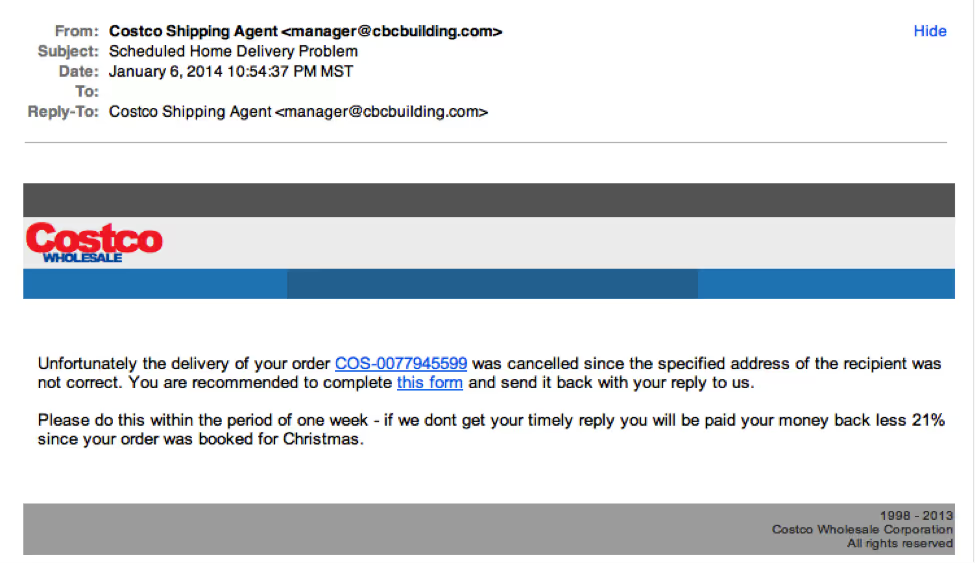
Find the answer here: 7 Ways to Recognize a Phishing Email: Email Phishing Examples
See also: White Paper: 5 Tips to Train your Workforce on Social Engineering
Here are 5 tips to properly train your workforce against social engineers:
1. Rethink Training
Training your employees when they are first hired, or having training sessions once a year isn’t cutting it anymore. The sessions are usually too long, the employees get bored, and most of the crucial security information doesn’t stick as a result.
Instead, do regular training quarterly, if not monthly. Focus on elements of social engineering and what employees can do to be aware of it. Repetition will help your employees to remember and apply their training in everyday situations.
Need to train your employees? Let us help!
2. Create security policies
The main problem organizations have with social engineering is their employees don’t know what to do if they find themselves in an uncertain situation. Create policies help your employees know the proper protocol for security. Established policies on handling data properly will help your workforce spot suspicious activity. Some specific policies may include:
- ID anyone trying to access off-limits areas
- Never use a USB unless directly obtained from the IT department
- Report lost/stolen badges within 12 hours of discovery
- Alert manager if you’ve encountered a social engineering situation
3. Make security part of the company culture
Implement a continuous training approach. For many employees, everyday work can cause them to forget crucial security information during trainings. Make social engineering training a part of the employee newsletter, send out regular emails, and put tips on bulletin boards.
If your employees are constantly being reminded to watch out for social engineering and mindful of what information they’re allowed to provide, they will know what to do when an attack occurs.
See also: Employee Training in Data Security: What You Should Do
4. Test your employees on social engineering
It’s often said that people learn best by doing. Testing your employees gives them an opportunity to practice combatting social engineering while helping you see what needs to be improved within your company’s security.
Create a social engineer team and have them test your own employees with some common social engineering tactics. Some things they could do are:
- Pose as a janitor and try to get to a secure room without a badge
- Dumpster dive for sensitive documents
- Leave USB devices around your site and track where they end up
- Try unlocked doors around the backside of buildings
- Pose as an IT person that needs to fix the network and see how close they can get to the server room
5. Train employees to be skeptical
A skeptical employee is a good employee. Your employees should feel safe to question something if it seems off to them.
Create an environment where employees aren’t afraid to report suspicious behavior. Your employees must feel comfortable questioning strangers.
If you don’t already have regular social engineering training in place, begin as soon as possible. Test all of your employees, including upper management.
If you don’t handle it now, you could be paying for it later.
For more information on social engineering and training against it, read the white paper 5 Tips to Train Workforce on Social Engineering.








.svg)