There’s only one way to avoid leaving ten-second holes in security. Encrypt card data at the exact millisecond of collection.
Hackers easily take advantage of encryption delays.
A common (and untrue) statement I hear from many businesses is, ‘My point of sale system encrypts all data that is stored, so I’m secure.’
True, most POS devices encrypt card data at some point after a card is swiped, but most take their sweet time, delaying encryption for millisecond, a second, ten seconds…or longer. To a business owner, ten seconds ‘til encryption sounds pretty safe, but to a criminal, that few seconds is plenty of time to snag card data from a computers memory or capture it from a hacker modified card swipe device.
Hackers can easily install memory scraping software that captures card swipe data during the delay from right under your nose, save it in a carefully coded database filled with thousands of other credit card numbers, and never alert you to their conniving presence. Who knows how long that could go on without a merchant finding out about it.
There’s only one way to avoid leaving ten-second holes in security. Encrypt card data at the exact millisecond of collection.
P2PE, one encryption process to rule them all
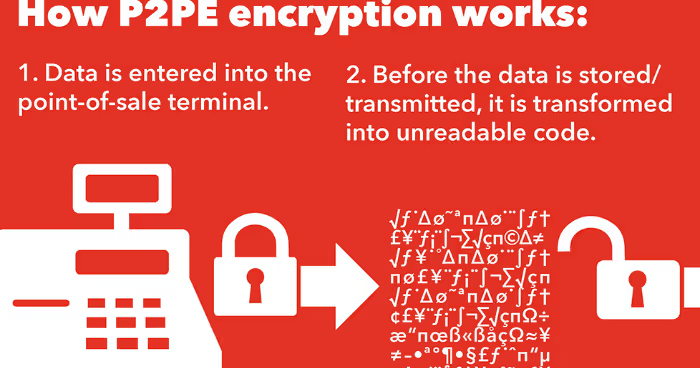
Point-to-point encryption (P2PE) is the combination of hardware and processes that encrypts customer credit/debit card data from the point of interaction until it reaches a merchant solution provider’s environment for processing.
Because card data is immediately encrypted as the card is swiped (or dipped), it prevents non-encrypted information from residing on the payment environment, even for one millisecond. Even if a hacker installed memory scraping software on the POS register, it would only pick up useless strings of encrypted card numbers with no way to decode them.
After encryption, the data is transferred to, decrypted by, and processed through the solution provider processor who is the sole holder of the decryption key.
Besides the significant boost in card data security, a validated P2PE solution offers merchants another noteworthy benefit. Compared to typical Payment Card Industry (PCI) Data Security Standard (DSS) requirements, the P2PE Self-Assessment Questionnaire (SAQ) is significantly reduced. At only 18 questions (vs. the average 80), P2PE scope reduction certainly lessens the annual PCI headache of most merchants.
Unfortunately for smaller merchants, the better the encryption, the more expensive to implement. To encrypt at the level I’m talking about, all existing POS hardware would need to be updated to P2PE validated solutions. Because of liability reduction, scope reduction, and security peace of mind, the extra upfront cost is worth it to many merchants.







.svg)